Please provide your technical specifications and project requirements for the Under Train Inspection Surveillance System. Our engineers will review your application and provide a detailed manufacturing quote, including exact pricing and lead times.



Under Train Inspection Surveillance System
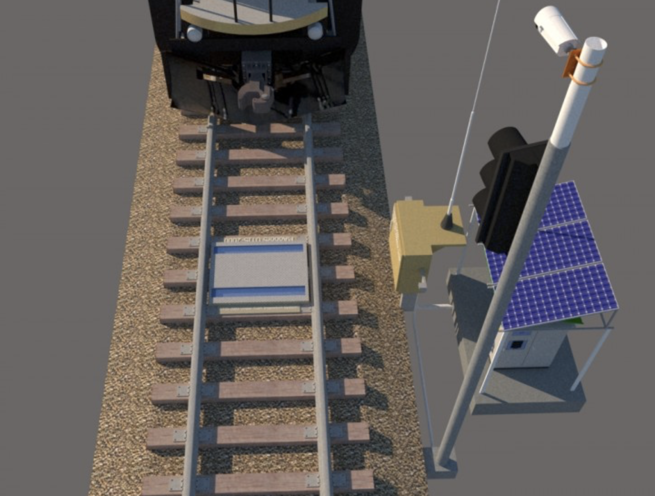
The Madoors USA MDRS-UTIS-2000 Under Train Scanning Imaging System is a 100% domestically produced, solar-powered, satellite-connected automatic under-train scanning system installed between the rails at stations and checkpoints — automatically detecting prohibited substances, drugs, weapons, and explosives attached under trains with quantum-type magnets by criminal and terrorist organizations, recording the complete train undercarriage image, reading the train number simultaneously, giving audible warning on detection, and transmitting the image and alarm wirelessly via satellite to a remote monitoring point. An integrated jammer trigger mounted on the train automatically activates at each stop — blocking iPhone and GPS signals to prevent the criminal network from locating their magnetically attached packages using Find My iPhone or GPS tracking apps before recovery.
Developed through Madoors USA R&D with Linescan and Areascan cameras installed between the tracks, computer and software processing, number reader camera, solar panels, inverters, battery kits, satellite antenna, sabotage alarm, perimeter cameras, and image recording system, the MDRS-UTIS-2000 is the comprehensive answer to the modern contraband method of magnetic attachment to train undersides — intercepting the criminal delivery before the material reaches its destination.
TECHNICAL SPECIFICATIONS
The MDRS-UTIS-2000 is installed between the rail tracks at station entrance and exit areas — the strategic positions where all trains must pass at low speed, providing optimal scan geometry and the security control environment required for effective contraband interception. The system placement at regular intervals along the rail line ensures that every train passing through the monitored network is scanned at multiple points — detecting packages that may have been attached at any point between scans.
The Linescan camera system builds a complete composite image of the train undercarriage as each carriage passes over the installed camera array — the line-by-line scan creates a continuous high-resolution image of the complete undercarriage from front to rear of each carriage. The Areascan camera provides additional area coverage for detailed examination of specific positions. Both camera systems work simultaneously to provide complete undercarriage coverage without gaps.
The automatic detection software analyzes each undercarriage scan image and compares it against the baseline profile of the clean train undercarriage — automatically identifying foreign objects attached to the train structure. When a foreign object is detected, the system immediately triggers an audible warning and transmits the detection image via satellite to the remote security monitoring point. This automatic detection eliminates the need for operator visual review of every carriage image — the system identifies anomalies automatically and only requires operator assessment when an anomaly is detected.
The number reader camera automatically reads the train carriage identification numbers and letters — correlating the number with the simultaneously captured undercarriage scan image and recording both together as a complete, time-stamped evidence package. This correlated recording provides the security forces with positive identification of the specific carriage carrying the contraband, directly supporting targeted intervention.
The power system uses solar panels to generate the energy required for continuous operation — the solar panels charge the battery kits that power all camera, computer, and communication systems. Inverters convert the 12V DC battery output to 220V AC for the camera and computer systems. This self-sufficient solar power system eliminates the requirement for grid power connection at remote track positions — allowing installation at any point on the rail network regardless of power infrastructure availability.
The satellite-controlled antenna system transmits images, detection alerts, and system status to the remote monitoring point wirelessly — providing real-time surveillance information to security force command centers at any distance from the installation position.
KEY FEATURES
Magnetic Attachment Contraband Detection
The specific operational principle the MDRS-UTIS-2000 addresses — the attachment of contraband packages to train undersides using quantum-type magnets in parking areas before departure — represents the modern evolution of rail smuggling that has emerged as road and pedestrian security has improved. The train's all-steel structure provides an ideal attachment surface for powerful rare-earth and quantum magnets, and the package remains securely attached throughout the journey without falling. The UTIS-2000 detects these magnetically attached packages by their foreign object profile in the undercarriage scan image — regardless of whether the package is metallic, organic, or wrapped in masking material.
Jammer Trigger — iPhone GPS Signal Blocking
The jammer trigger mounted on the train that automatically activates at each stop is the counter-intelligence feature that neutralizes the criminal network's package tracking method — criminal organizations attach iPhones running Find My to packages so they can locate and retrieve them at the destination. The jammer blocks all iPhone and GPS signals in the vicinity of the train at each stop, preventing the criminal network from knowing where their packages are located and interrupting the Find My app signal that would guide their recovery operatives to the package. Security forces can therefore intercept the criminal recovery attempt — arresting the operatives as they attempt to retrieve the packages.
100% Domestic R&D Production — National Technology
The 100% domestic production through Madoors USA R&D development confirms national technology sovereignty for this security application — all software algorithms, camera systems, satellite communication, and integration design are developed and manufactured within national jurisdiction. This domestic development ensures that the security capabilities and detection algorithms of the system are not subject to foreign technology restrictions or compromise.
Automatic Detection & Satellite Transmission — Real-Time Alert
The fully automatic detection without operator review of every image — the system autonomously identifies foreign objects and triggers alerts — combined with immediate satellite transmission to the remote monitoring point provides the real-time security response capability required for effective contraband interception. The time between train arrival at the scanning position and remote monitoring center alert is measured in seconds — providing security forces with the maximum available reaction time to intercept the package before the train departs.
Solar-Powered Self-Sufficient — Remote Track Installation
The solar panel and battery kit self-sufficient power system allows installation at any position on the rail network — no grid power connection is required. This power independence directly enables installation at the most strategically effective positions on the rail line rather than only at positions with available power infrastructure. The continuous battery backup ensures uninterrupted operation during low solar generation periods including cloudy days and nighttime.
Train Number Reading — Correlated Evidence Recording
The automatic number reader camera that simultaneously records the train carriage identification alongside the undercarriage scan image creates a complete, legally usable evidence package — the detection image is correlated with the specific carriage number, the timestamp, and the installation location. This correlated evidence directly supports the criminal prosecution of smuggling operations — the image provides proof of the package's presence under the identified carriage at the recorded time and location.
Sabotage Alarm & Perimeter Security
The sabotage alarm system and perimeter cameras protect the UTIS-2000 installation against physical tampering or destruction by criminal organizations aware of the scanning system — detecting and recording any approach to the installation outside normal maintenance schedules, transmitting emergency alerts to the remote monitoring point, and creating an evidence record of any tampering attempt. This multi-layer physical security ensures that the scanning system remains operational and provides evidence even if tampering is attempted.
Station Entrance & Exit Installation — Strategic Positioning
Installation at station entrance and exit areas provides the most effective scanning coverage with the minimum number of installations — every train must stop at the station, providing the extended stationary or slow-speed scanning time that maximizes image quality, and the station security environment provides the best conditions for rapid security force response to a detection alert. The entrance scan detects packages attached at the previous stop, and the exit scan confirms clean departure.
SYSTEM ARCHITECTURE
Rail-Mounted Camera Array — Linescan and Areascan cameras installed between the rails at the confirmed installation positions. Scan geometry optimized for the specific rail track gauge and train undercarriage clearance height.
Computer & Detection Software — Processing unit installed at the installation site within the protective housing. Software performs automatic undercarriage image analysis, foreign object detection, and alert generation. Train number reading software correlates carriage identification with undercarriage images.
Solar Panel & Battery Power System — Solar panels provide daytime generation. Battery kits store energy for nighttime and low-light operation. Inverters convert 12V DC battery output to 220V AC for camera and computer systems.
Satellite Communication Antenna — Transmits undercarriage images, detection alerts, train identification data, and system status to the remote security monitoring center. Wireless transmission eliminates cable infrastructure requirements at remote track positions.
Train-Mounted Jammer Trigger — Automatically activates at each train stop. Blocks iPhone, smartphone, and GPS signals in the vicinity of the train. Prevents criminal network GPS tracking and Find My app package location during the interception window.
Sabotage Alarm & Perimeter Cameras — Detect and record unauthorized approach to the installation. Transmit emergency alerts and perimeter images to the remote monitoring center.
DEPLOYMENT SCENARIOS & USE CASES
Madoors USA MDRS-UTIS-2000 Under Train Inspection Surveillance Systems are deployed at any rail infrastructure position requiring automatic under-train contraband detection.
- National rail network inter-city route under-train scanning
- Border crossing rail checkpoint under-train inspection
- Major city station entrance and exit scanning systems
- Rail freight terminal under-train contraband detection
- High-speed rail network checkpoint scanning systems
- Tourist and passenger rail route security scanning
- Military logistics rail route under-train monitoring
- Critical infrastructure rail access security scanning
- International rail border crossing contraband detection
- Regional railway network counter-smuggling scanning
- Port rail connection under-train inspection systems
- Airport rail link security checkpoint scanning
- Underground and metro network security inspection
- Railway maintenance depot departure scanning
- Any rail infrastructure position requiring automatic solar-powered under-train contraband detection with satellite transmission
- Category: Under Vehicle Surveillance Systems